The Unfriendly Internet: Cyber Attacks and Your Defenses
Originally published Winter 2018/2019
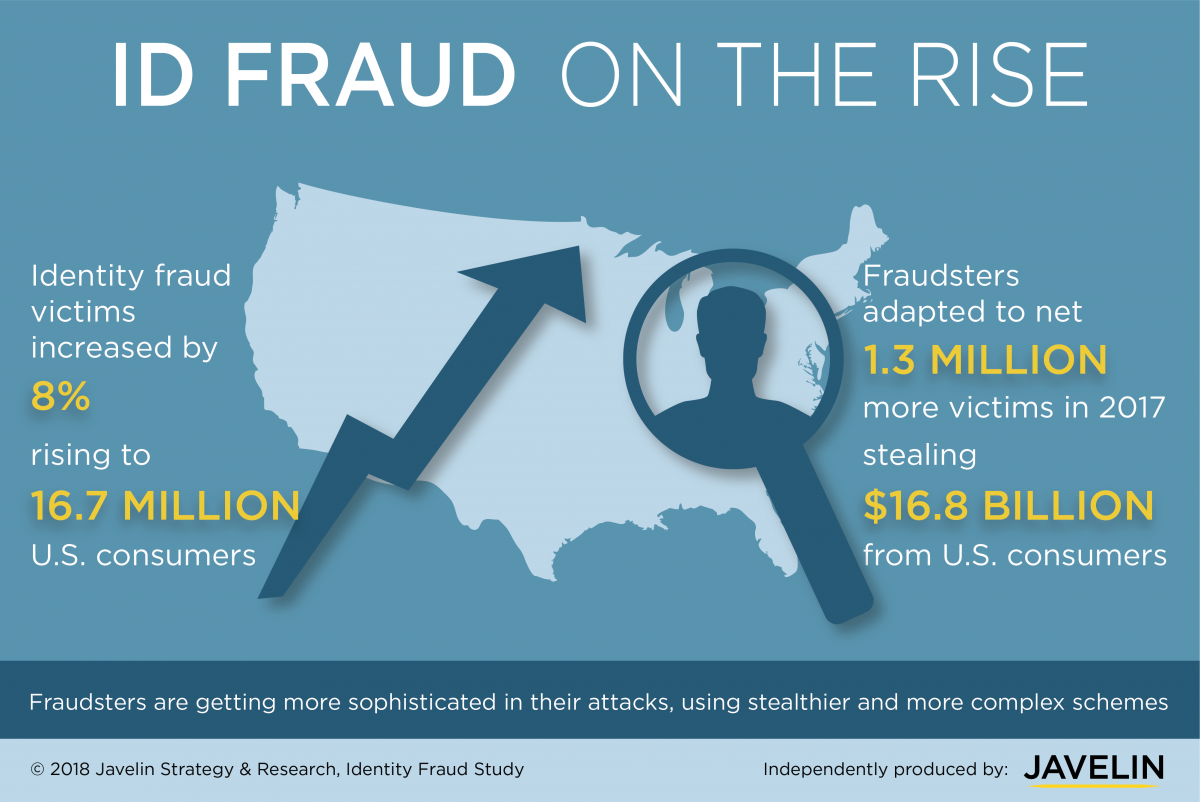
A little over a year has passed since, Equifax, a leading credit reporting agency, reported a data breach event that impacted around 143 million U.S. consumers. With the holidays upon us, and the resulting spike in consumer Internet activity, it’s a good time to review possible cyber exposure, and some ways can protect yourself.
Your Insurance Policy:
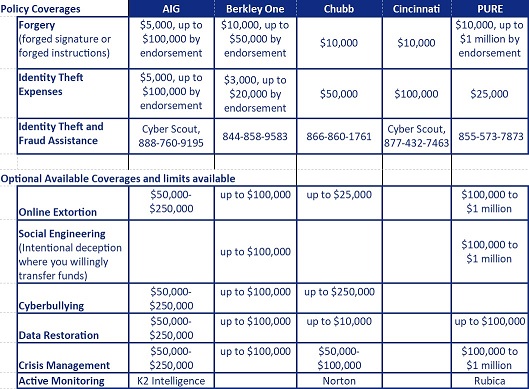
Many people are not aware of the cyber coverage that may be available under their residence policies. We have compiled and summarized the following currently available coverages from in- surers that represent the majority of Chartwell clients; AIG, Berkley One, Chubb, Cincinnati, and PURE. (Note that each insurer may define these exposures differently.)
1) Unauthorized use of credit cards, debit cards, and fraudulent electronic fund transfers. This is actual reimbursement for loss sustained, subject to the policy deductible;
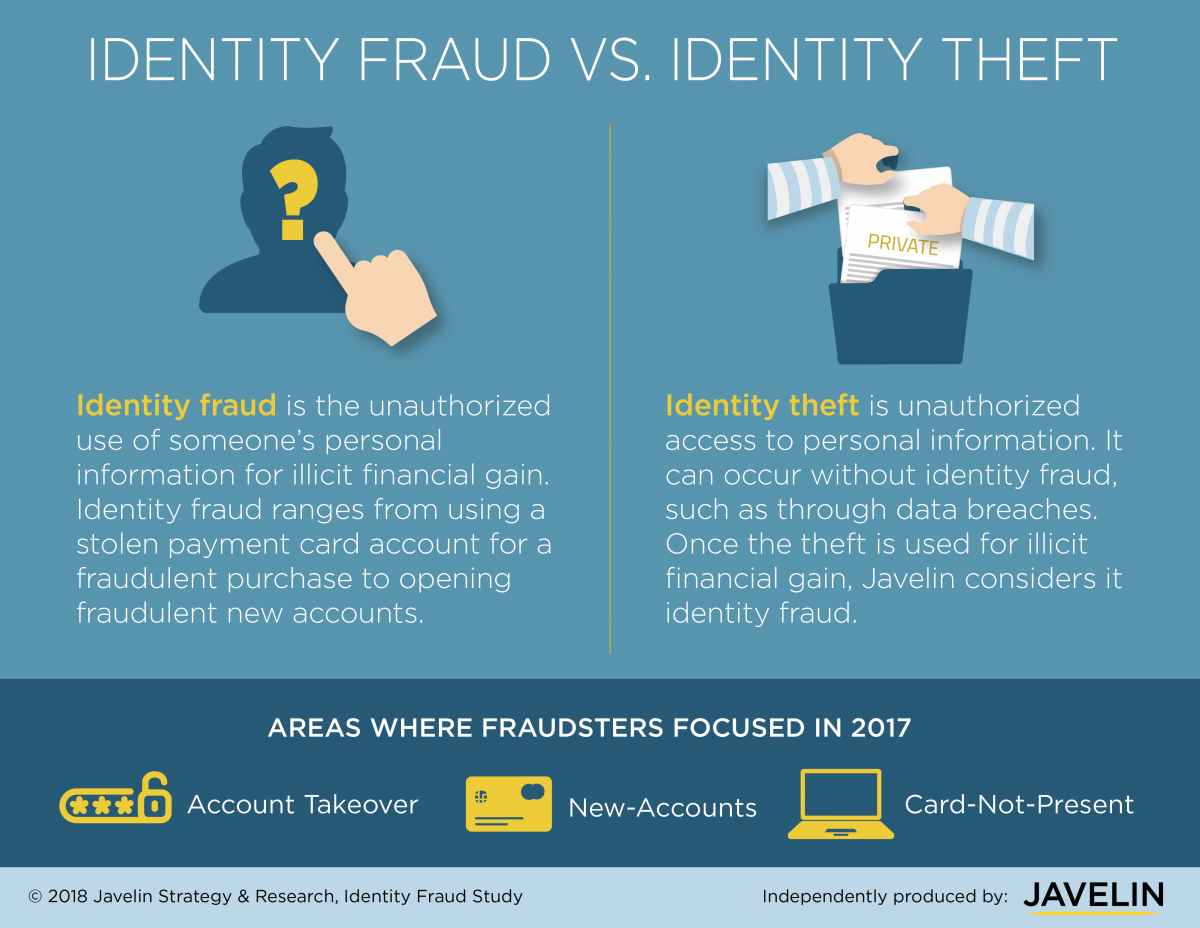
2) Identity theft expenses coverage will reimburse a policyholder for money and securities that are stolen, and expenses incurred as a result of someone appropriating your identity. Examples of expenses included under this coverage are reimbursement for lost wages, costs for notarizing affidavits, costs for certified mail, and other costs to clear and rehabilitate the credit record of the identity theft victim. If you believe you are a victim of identity theft, each insurer offers complimentary helplines.
In addition to those usually automatic coverages, some insurers have introduced tailored cyber coverages that are available by endorsement, generally for an additional premium. These include:
1) Online extortion, where someone threatens to lock your com- puter system unless you pay them money, also known as ransomware.
2) Social Email Engineering. In what are becoming increasingly sophisticated scenarios, cyber attackers intercept otherwise legitimate emails, and insert fraudulent payment information. This is sometimes referred to as a "phishing" attack. Because the victim has actively and willingly transferred funds to the cyber attacker, it is harder to obtain insurance coverage. Currently, only Berkley One and PURE offer this protection.
Ways to avoid this include: a) Never accept wire transfer or payment information solely via email; b) Confirm the payment information by phone or fax through connections known to be authentic; c) Don’t call the phone number on the email with the payment instructions.
3) Cyber-bullying. This is any type of harassment or bullying that occurs through email, a chatroom, instant messaging, a website (including blogs), or text messaging. While initially this was perpetrated by juveniles on other juveniles –like physical bullying and harassment- it can now happen to an adult who unwittingly gains national attention because of something they allegedly said or did. The coverage can help mitigate the cost of wrongful termination, false arrest, wrongful discipline in an educational institution, or diagnosed debilitating shock, mental anguish or mental injury.
All cyber coverages, whether automatic or elected, typically also in- clude the cost of data restoration, and crisis management expenses.

Steps you can and should take for your cyber protection:
1) Credit Monitoring. Pull your credit reports. Federal law allows you to get a free copy of all three credit bureau reports at annualcreditreport.com. Check for any errors, and make sure that all listed loans, and credit cards belong to you. Equifax is offering free access to their TrustedID Premier monitoring services for anyone who has used Equifax in the past, whether or not they were affected by the recent data breach.
2) Credit Freeze. Federal legislation passed in May 2018 requires the credit reporting agencies to provide credit freezes free of charge. A “credit freeze” means no one can access your credit report. That’s the good news; the less good news is that you have to do it yourself by visiting these agency sites:
Experian
https://www.experian.com/blogs/ask-experian/credit-education/ preventing-fraud/security-freeze/
Transunion: This includes information on downloading their smart phone app.
https://www.transunion.com/credit-freeze
Equifax:
https://www.equifax.com/personal/credit-report-services/
Password Protection
Access to your cyber information starts with the password, and cyber attackers are almost supernaturally adept at breaking passwords. The following is adapted from a New York Times article by personal finance correspondent Ron Lieber, January 26, 2018.
The password guidelines laid out by NIST National Institute of Standards and Technology are written for the government and leveraged by IT professionals at big companies. But these are lessons we can all take from them with our everyday online habits:
• Use four or five random words strung together with spaces be- tween them. According to the recent data and research, your best chance of keeping your password from getting cracked is to use a string of a few unrelated words separated by spaces. So a crazy jumble of words may just be what helps keep your information safer. Of course, as a user you’re limited to what an entity or financial institution requires you to do and some may still make you use special characters.
• Make the passwords easy to remember. If you are able to remember your passwords, you won’t have to change them all the time or leave them written on post-it notes or notepads, which can get lost or end up in the wrong hands. Top infosec [information technology security] professionals also recommend that you don’t use the same passwords for multiple websites. So even those of you with great memories likely can’t keep all the websites and logins straight in their head. So what are some options? You can look into password management tools that help you with storing passwords, such as LastPass and 1Password and Password Safe https:// pwsafe.org/
• Don’t change your passwords unless you suspect your information has been breached. Turns out that changing passwords frequently can actually just give cyber criminals a glimpse at potential patterns in your passwords, allowing them to crack them more quickly. No need to change them every so often anymore just because.
• Use multi-factor authentication (MFA) when you can. Also commonly known as two-factor authentication, this is available on many larger sites and will require an extra step (such as identifying additional information or getting a text with a code to enter). It’s worth using if a website offers it, since it means someone needs more than just your password to get into your account—especially when accessing your account on a new device.
General Security Information:
•Are cyber-voice assistants like Alexa, Siri, or Google Assistant spying on the user? Are they capable of spying? A journalist from CNBC asked the virtual entities that question. The answers were negative, but some may feel it prudent to switch these features off.
Click Here to Be Redirected to the Article
How to Turn off Siri
https://appletoolbox.com/2017/10/how-to-turn-off-siri-in-ios-11- its-easier-than-you-think/
• The camera at the top of your computer screen is great for Facetime, but cyber hackers can gain access to the camera and look at you and into your room: Just to be safe, place a post-it note over the lens.
• A webpage on a California company’s website to test the location of your cellphone contained a bug that allowed a doctoral re- searcher to look up the location of a U.S. cellphone by punching in the 10-digit number: To prevent this, turn off your phone loca- tion services by going to settings and select privacy.
• Digital photos often contain hidden details of the location, so an unwitting on-line posting could reveal the photographer’s wherea- bouts: Remove EXIF data from photos so your photos posted online don’t contain location information.
https://www.howtogeek.com/203592/what-is-exif-data-and-how- to-remove-it/
• Avoid public wi-fi unless you are working through a secure channel on your tablet or laptop.
Summary
It used to be that home security involved reliable physical deterrents: sturdy locks on all entrances and windows, movement detectors, noise detectors, and an alarm system triggered by the presence of intruders and connected to a central station which in turn would alert emergency services. Times have changed. Criminals looking to invade your home and your privacy to steal items of value can now gain entry through the invisible radio waves of the worldwide web. The extraordinary benefits of Wi-Fi in the home and in the public space can be upended to aid and abet sophisticated thieves who are no longer limited to what they can carry away with them. Anyone who is active on the Internet — and that includes anyone reading this bulletin— should review their own exposure to cyber-crime and take appropriate steps to mitigate it.
Chartwell Bulletins are produced by Chartwell Insurance Services, Inc., an independent insurance broker specializing in the personal asset protection of high-net-worth individuals. Chartwell Bulletins address issues of general interest and since coverages vary by company and by state should not be taken as an interpretation of a particular policy or advice on any individual situation.
A representative of Chartwell Insurance Services will be pleased to discuss all aspects of your personal insurance.
Contact: Rebecca Korach Woan 312-645-1200 or rwoan@chartwellins.com